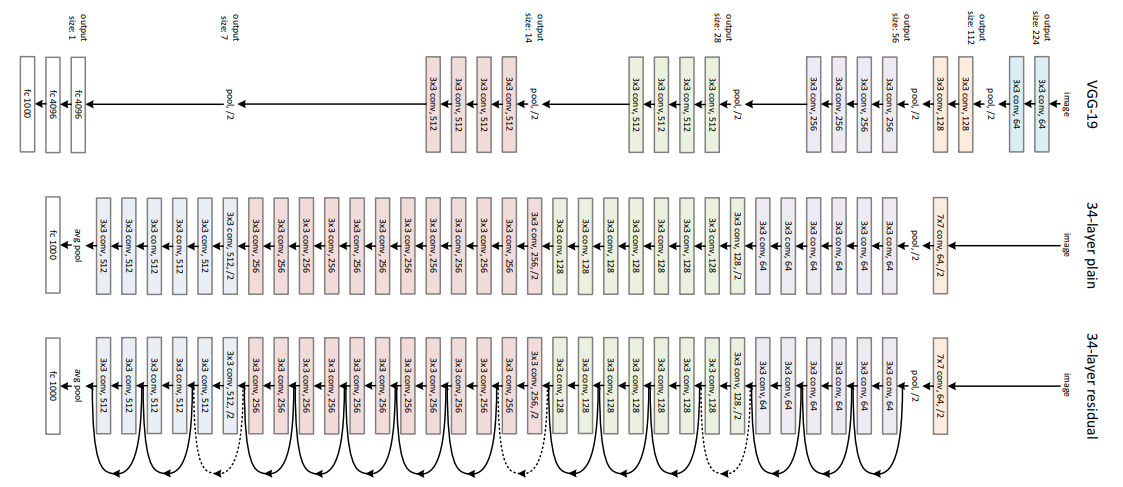
The representation of model architecture image for ResNet-152, VGG-19,... | Download Scientific Diagram

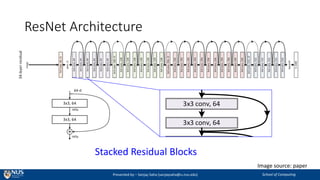
neural networks - Are there any weight matrices of residual connections in ResNet? - Cross Validated
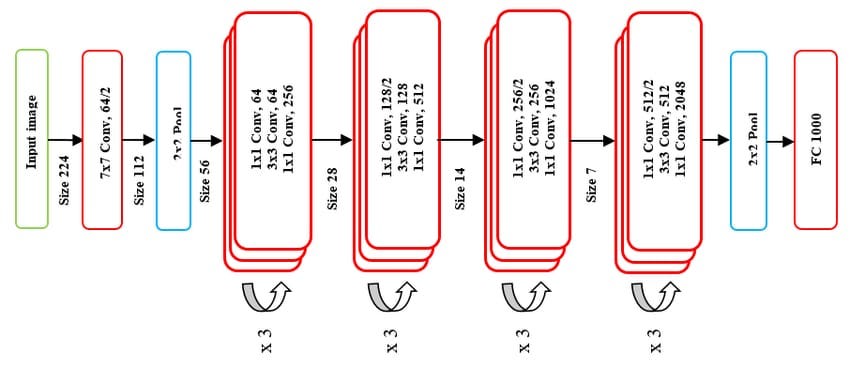
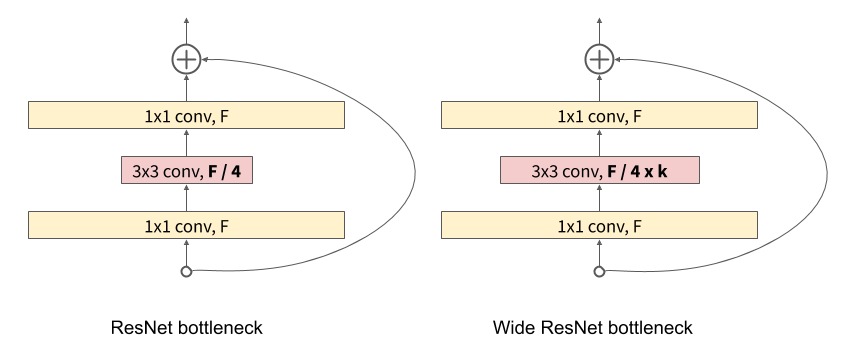
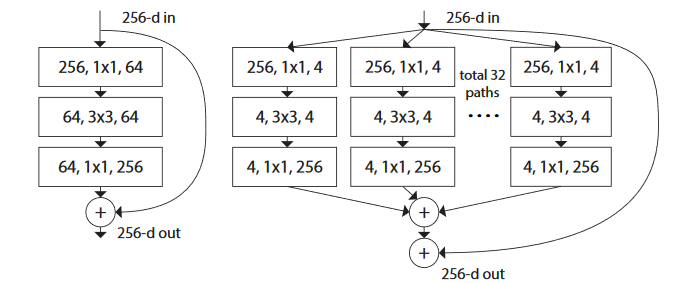
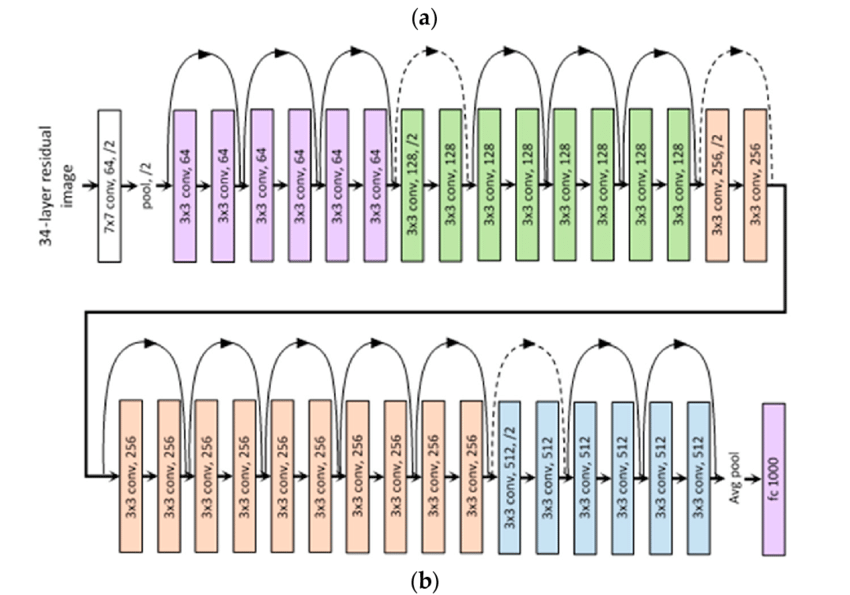
The Annotated ResNet-50. Explaining how ResNet-50 works and why… | by Suvaditya Mukherjee | Towards Data Science

The architecture of ResNet-50-vd. (a) Stem block; (b) Stage1-Block1;... | Download Scientific Diagram

Figure 1 from Malicious Software Classification Using Transfer Learning of ResNet-50 Deep Neural Network | Semantic Scholar




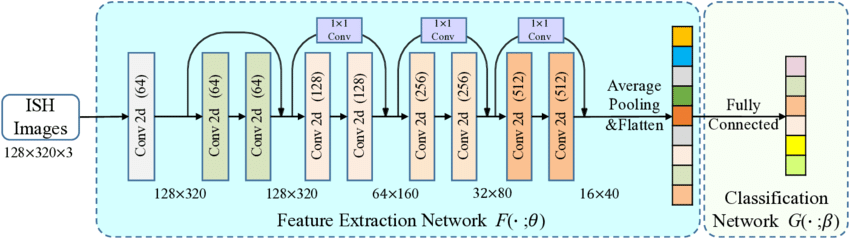
![PDF] ResNet-50 and VGG-16 for recognizing Facial Emotions | Semantic Scholar PDF] ResNet-50 and VGG-16 for recognizing Facial Emotions | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/77bb47c2fee25982cf0ac69521239b9b528a4b28/2-Figure1-1.png)


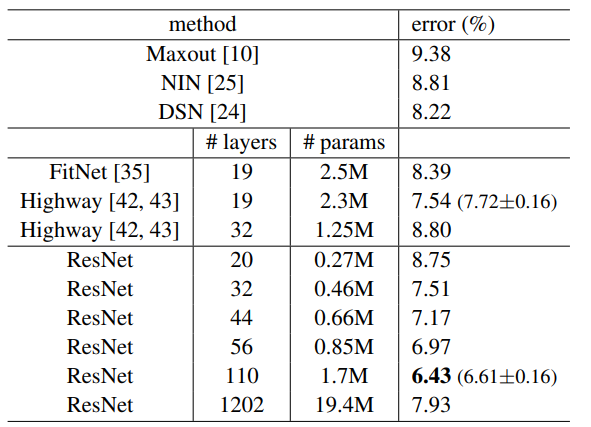



![PDF] Deep Residual Learning for Image Recognition | Semantic Scholar PDF] Deep Residual Learning for Image Recognition | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/2c03df8b48bf3fa39054345bafabfeff15bfd11d/5-Table1-1.png)